Packet Espionage: A Story of Encapsulation
A thrilling spy adventure on how packets transverse networks. This is a story of a spy network that uses encapsulation to secure their payload. How will Agent Packet and his team get their information to its destination?
5/19/20253 min read
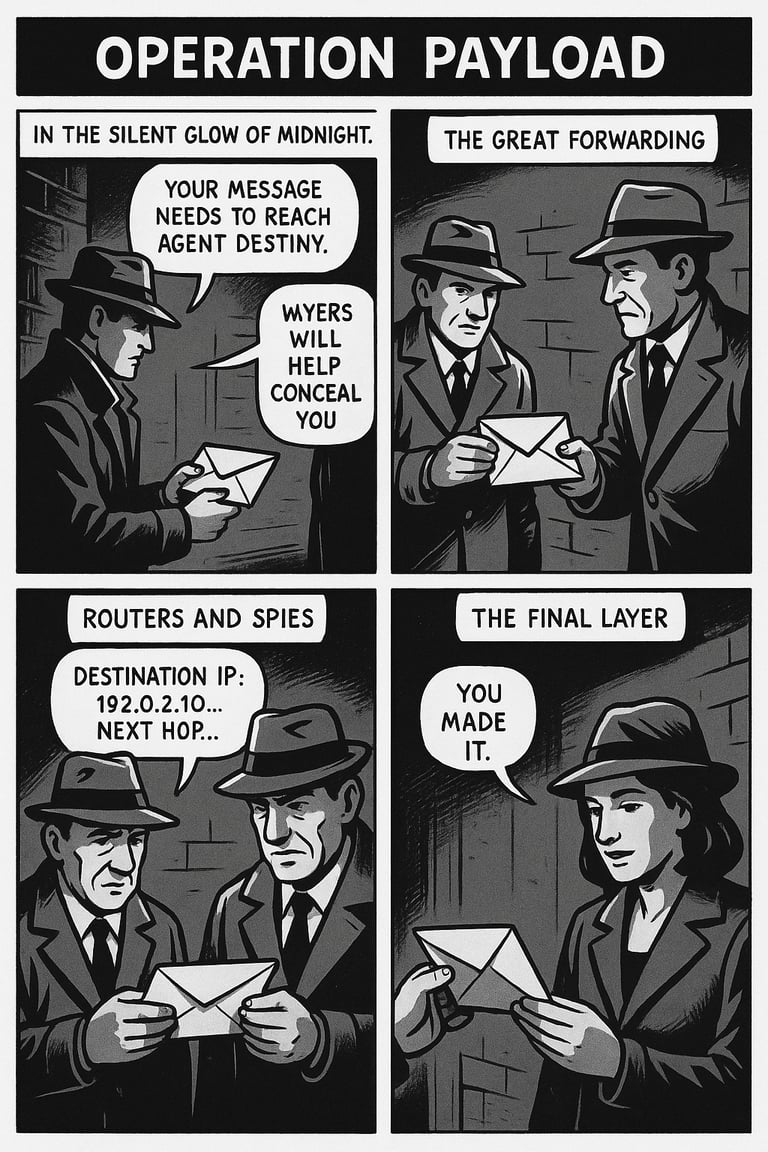
Chapter 1: Agent Packet
Agent Packet nervously stood at the back entrance of Network HQ. Having received his mission payload, he gripped it tightly. This wasn’t just information—it was critical intelligence for their mission. His handler, Major App, gave him his final instructions...
> “Your message needs to reach Agent Destiny at IP 192.0.2.10. It's far too risky to go directly. The other Agents will help conceal you. Each one knows a bit of the route, but only the last Agent knows the target. You must get to them, and then get this to Agent Destiny.”
Packet nodded. He understood the drill: Encapsulation.
Major App handed him the first envelope—his application payload.
Then came Agent Tran. She controlled the transmissions, and where it would go. She wrapped the payload in a new envelope marked with port numbers, sealing it with the TCP label. He was going to the docks.
> “Stick to our reliable delivery routes,” she whispered. “And watch out. This is a large message. I'll mark the segments so in case you get broken up we'll be able to reassemble everything.”
Next, the Agent Net. He wrapped the parcel again, this time adding source and destination addresses. But the source was his own address, assuring that the lower levels of the agency remained concealed and safe. Packet knew by looking at the destination address that he'd have to see a few other of Agent Net's coworkers along the way before reaching his destination at the docks. Visiting one by one, they wrapped their own label over the parcel, with their own source address. This would be useful to the agent with the return data after Agent Destiny completed her mission.
Finally, Agent Packet came across Agent Data, who encased the entire packet with a frame—which contained the code, or MAC address, of the current hop.
> “You’re off,” whispered Data. “First stop, the local switch.”
Chapter 2: The Great Forwarding
Packet arrived at the first node: a tiny, yet powerful agent called a switch. The switch didn’t read the IP address. Instead, it peeled open just the outermost wrapping—looked at the MAC address, and said:
> “Hmm... this isn't for me. But I know who owns this MAC.” He pointed down the road. "Port 3."
And off Packet went, sprinting to the next layer: Routing.
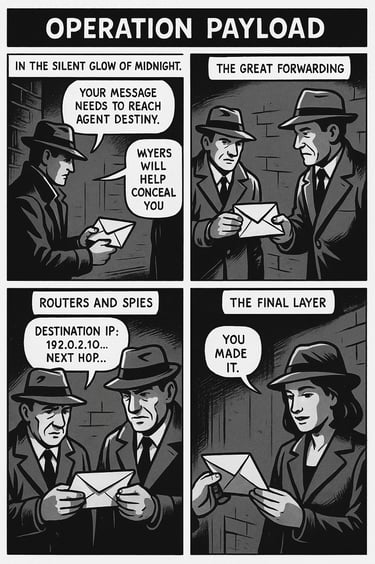
Chapter 4: The Final Layer
Hop by hop, forwarding continued. Each Router agent was the same: organized, quick-witted, and thorough.
With each new Router agent, they swapped MAC addresses as they passed him along. Each time, Packet lost a frame and got a new one. But his core—his IP and TCP identity—remained intact. This was the core information to get to Agent Destiny.
Finally, he arrived at the destination subnet, a small network of agents that worked like an independent cell. Their router forwarded him to the target's Local Area Network. The local switch agent, peaked into the envelope to check the MAC address. The destination MAC matched one of its own ports, sent him directly to…
Agent Destiny.
> "For you ma'am," Agent Packet said, as he handed over the envelope.
She peeled off each layer carefully:
- First, the data frame—
> "Not mine."
- Then, the network IP envelope—
> "Ah, addressed to me."
- Then, the transport envelope—
> "Yes, this is my correct port..."
- Finally, the payload—pure, unencrypted intelligence.
> "Good work, Agent," Destiny said as she looked through the information.
Epilogue: Mission Complete
Agent Packet’s journey was over. He had survived— all to deliver one message across a hostile, complex network. Should Agent Destiny need to respond, another Agent would traverse the same path he did. It's difficult, but important work ensuring the right information goes to the right agent, and he was proud of their efforts.
Chapter 3: Routers and Spies
His next stop was a router—grizzled and sharp-eyed. This one did read the IP address under the frame Data had placed on the parcel.
> “Hmm. Destination IP: 192.0.2.10. Not local. Let me check the routing table…”
He rifled through his notes: a big, heaving tome of all current known locations and their addresses.
> “Here's your best path: Next hop 203.0.113.1 via interface G-0/1.”
He stripped off the old MAC address layer and wrapped Packet with a new one—his MAC as source, and the next router’s as destination.
> “Next hop will know what to do,” the router said, giving Packet a nod and sprinted towards G-0/1.